Be the first to know.
Get our cybersecurity weekly email digest.
cybersecurity
Engineers Wiki. Most Asked Questions.
Explore IoT security solutions with insights into the threat landscape, secure architectures, and best practices for engineers building resilient connected systems.
Raspberry Pi 5 GPIO Pinout: Theory and Practice for Engineers
By Muhammad Sufyan.
12 minutes read.
Raspberry Pi Zero 2 W Pinout: Comprehensive Guide for Engineers
By Muhammad Sufyan.
12 minutes read.
Half Adder Circuit—Theory, Design, and Implementation
By Muhammad Sufyan.
11 minutes read.
Modbus RTU vs TCP: A Comprehensive Comparison of Industrial Protocols
By Muhammad Sufyan.
14 minutes read.
ORGANIZATIONS. SHAPING THE INDUSTRY.
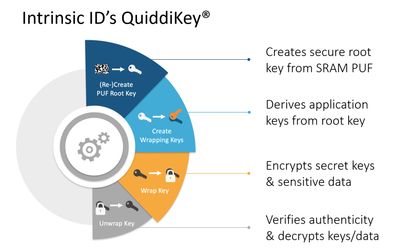
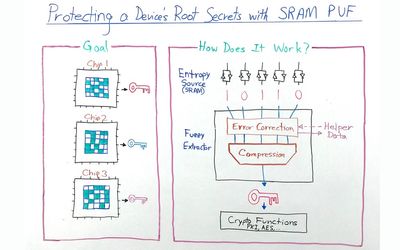
Intrinsic ID
Semiconductor
Securing the IoT with the World's Top PUF Technology. Authenticate Everything.
16 Posts
Quest Global
Aerospace & Defense, Automotive, Energy, Hi-Tech, MedTech & Healthcare, Rail, Semi-conductor & Communications
We believe engineering has the unique opportunity to solve the problems of ...