The Hidden Cost of Manual Builds: Why Teams in Regulated Sectors Must Embrace CI/CD
This article explores how automated CI/CD pipelines replace fragile manual build processes with reproducible, auditable workflows that improve compliance, reduce defects, and accelerate development in regulated embedded systems
In medical devices, automotive systems, and industrial automation, software is a regulated component of the product itself. That changes what "good enough" means for a build process. A binary you cannot reproduce is a binary you cannot validate, and a build environment you cannot audit is a liability in every certification cycle you run.
Despite this, many embedded teams still operate with manual or loosely controlled build processes: toolchains installed directly on developer machines, no enforced versioning, and test and analysis steps that run inconsistently, if at all. The problems this creates are well understood in theory but chronically underestimated in practice. Build reproducibility directly affects validation scope, certification timelines, and release predictability.
CI/CD pipelines provide a structured path out of this. Automated builds, integrated analysis, and containerized environments together standardize execution, generate compliance evidence continuously, and reduce the audit burden at release time. Adoption does not require a dedicated DevOps team or a full infrastructure overhaul. Teams can start with automated builds alone and extend the pipeline incrementally from there.
The Real Price of "Good Enough" Build Processes
The most immediate problem with uncontrolled build environments is variability. When each developer maintains their own toolchain configuration, subtle differences accumulate, from compiler versions to library paths, optimization flags, and environment variables. Two developers building the same commit may produce different binaries. In most software contexts, this is inconvenient; in regulated development, it is a compliance failure waiting to materialize.
Unqualified or non-certified toolchains compound this. During audits, teams must self-justify tool behavior, documenting that a given compiler version produces correct output under the conditions used. This is significant validation work that certified toolchains eliminate by shifting that burden to a qualified third party.
The downstream effects are predictable. When defects are found late, as they inevitably are when analysis and testing run manually or infrequently, debugging requires first reconstructing the environment the defect occurred in. That reconstruction may not be possible if the environment state was never captured. Troubleshooting build and pipeline failures alone can consume up to 40% of development time, time that should be going toward innovation, testing, and actual feature work.
Audit preparation in these environments is largely manual. Engineers assemble evidence from disparate sources: build logs from one system, test results from another, and analysis outputs from a third. Certification timelines extend unpredictably not because the product is unsafe but because the documentation trail is incomplete or inconsistent. Engineering effort shifts toward rework and environment management rather than toward the product.
Anatomy of an Embedded CI/CD Pipeline
A well-structured embedded CI/CD pipeline follows a 5-stage, fixed sequence:
Code → Build → Analyze → Test → Deploy
Code commit triggers build, which feeds into static analysis, which gates automated testing, which then produces validated artifacts for deployment. Each stage is automated, version-controlled, and produces structured outputs.
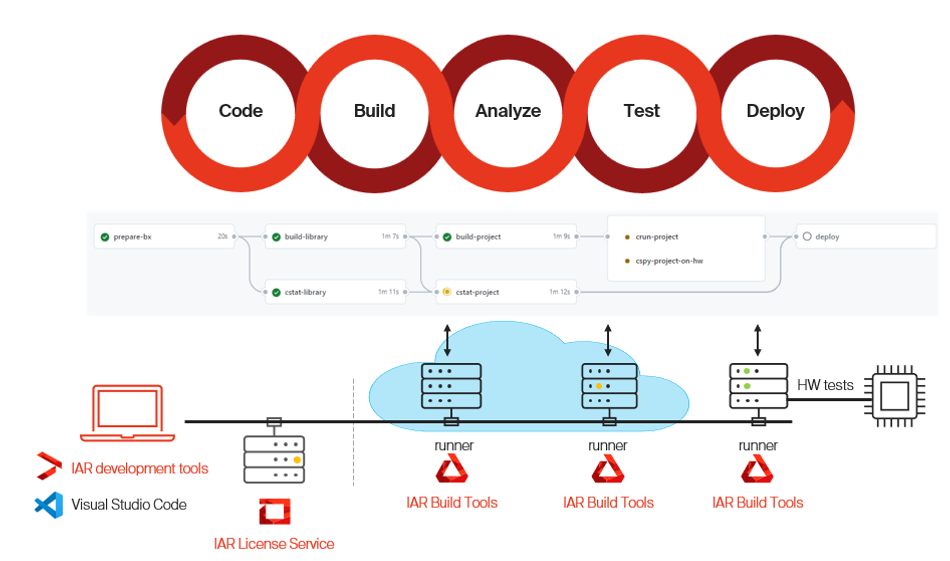
The value of this goes beyond speed. The pipeline becomes a system of record. Build logs, analysis reports, and test results are generated automatically on every run, linked to the specific commit that produced them. The path from source code to deployed binary is fully traceable and reproducible. When a regulator asks for evidence that a given artifact was built from a known state and tested against defined criteria, that evidence exists and is organized.
Continuous validation through static analysis and runtime checks, integrated directly into the pipeline, shifts defect detection to the earliest possible point. A coding standard violation found at commit time costs minutes to address. The same violation found during integration testing can cost days.
Containerization: The Foundation for Consistency
Reproducibility requires that the build environment itself is controlled and versioned. Containers solve this directly. Packaging the toolchain, compiler flags, analysis tools, and all dependencies into a versioned container image means every pipeline run, whether on a developer's workstation, a cloud runner, or an on-premises CI server, executes in an identical environment.
This has a direct compliance benefit. Qualification effort can be focused on the container image rather than each developer's local setup. Once the toolchain configuration inside a container is qualified, that same configuration runs identically everywhere, eliminating the risk that a local toolchain update silently changes the environment under assessment.
When TÜV-certified toolchains are packaged inside containers, the certified boundary is clear and fixed. The container image itself becomes auditable: its contents are known, its version is tracked, and its behavior is consistent across infrastructure.
Isolated container environments also provide a security boundary. Dependencies cannot drift silently, and there is no ambiguity about which version of a tool was used for a given build.
Performance and Quality Gains You Can Measure
The shift to automated, containerized pipelines produces concrete gains. IAR Build Tools on Ubuntu deliver build times roughly twice as fast as equivalent Windows-based workflows, and C-STAT static analysis runs approximately 3.5 times faster. Across build and debugging effort combined, automated analysis with pre-qualified toolchains reduces total time by 50 to 80 percent.
C-STAT enforces MISRA C/C++, CERT C/C++, and CWE coding standards across every pipeline execution. At that speed advantage, comprehensive standards coverage stops being a bottleneck and becomes a continuous, low-friction part of the build process.
Quality metrics follow a similar pattern. Continuous enforcement of coding standards on every commit, rather than periodic manual review, produces roughly a 41% reduction in defect injection rates. Defects caught earlier in the pipeline require significantly less effort to fix, and downstream testing loads decrease as a result.
These are not marginal improvements. For teams operating under release pressure in regulated markets, halving build and debug time while reducing late-cycle defects directly affects both certification timelines and product quality.
Starting Small: Incremental Adoption
CI/CD adoption in embedded development does not require a dedicated DevOps team or a large infrastructure investment. The risk of incremental adoption is low: starting with automated builds does not disrupt existing workflows or trigger re-validation requirements.
The practical entry sequence is to automate builds first, capturing the toolchain configuration and making builds reproducible. Then, introduce static analysis as a pipeline gate. Afterwards, you add automated testing. At each step, containerized environments simplify setup and make the expanded pipeline portable. Teams retain ownership of their pipelines throughout. The incremental approach also means compliance evidence accumulates progressively rather than requiring a large documentation effort at the end of a release cycle.
Enabling Embedded CI/CD with IAR
IAR's toolchains are built for automation-first workflows. IAR Build Tools are headless, scriptable, and integrate with standard CI platforms including GitHub Actions, GitLab CI, and Jenkins. Static analysis through C-STAT and runtime verification through C-RUN run inside pipelines without manual intervention. Toolchains pre-certified to IEC 61508 (industrial automation), ISO 26262 (automotive), and IEC 62304 (medical devices) reduce the validation work teams must do themselves during certification.
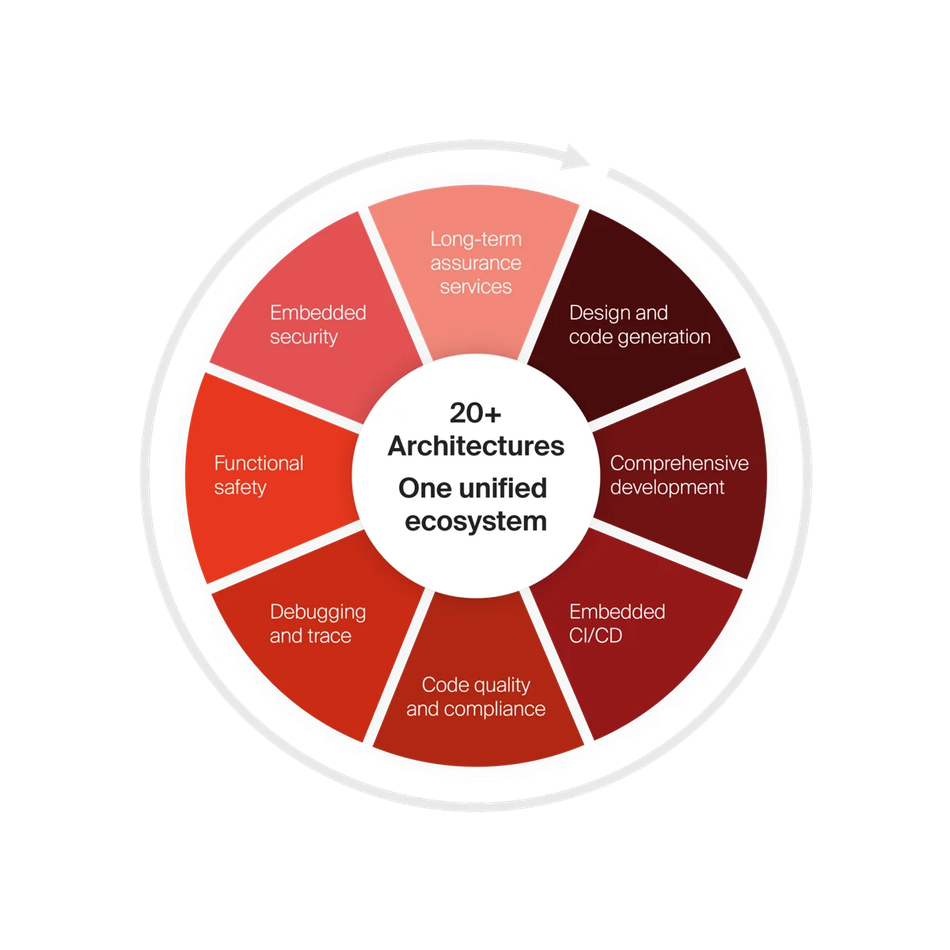
Cloud-based licensing removes the constraint of node-locked licenses tied to specific machines, enabling consistent workflows across local development, cloud runners, and on-premises systems. Support for over 20 processor architectures means teams working across device families can standardize on a single toolchain ecosystem without being forced into architecture-specific tool fragmentation.
IAR Embedded Trust extends pipeline automation to firmware security. Automated signing and encryption within the pipeline integrates security requirements from CRA and UN R155/R156 directly into the build process rather than treating them as post-build steps.
Conclusion
Build reproducibility in modern embedded development is the foundation that compliance work depends on. Automated workflows, built on certified toolchains, ensure consistent execution, validation, and traceability from commit to deployed artifact. An environment that cannot consistently reproduce a binary cannot validate, certify, or maintain it.
Regulatory expectations around software development processes are continuing to formalize across medical, automotive, and industrial sectors. Teams that establish reproducible pipelines now gain direct control over their development timelines and compliance readiness, rather than discovering gaps under deadline pressure during certification. The cost of manual builds is always higher than it appears, and it compounds with each release cycle.